13 Security Tips to Make Your Salesforce More Secure
Intro
With the ever-growing need for cloud computing or cloud-based services, it's often wise to implement a layer of security practices to prevent cyber risks or human errors. One of the business goals is to reduce hacking or exposing vulnerabilities of your system.
Here is a list of security measures you can take to make your Salesforce more secure.
MFA (Two-Factor Authentication)
Include an additional layer of protection to your customer accounts with multi-factor verification. Visit the MFA Page. With MFA, you can mandate 2-factor authentication (SMS, app, email etc.). Admin users can simply set this up by following this guide HERE.

RELATED: 10 CRM Implementation Steps for Company Success
Limit Admin Access
This sounds obvious, but sometimes laziness can compromise security. An organization should be strict about who should be given admin access. It should be even detailed enough to restrict what type of admin access is needed for each person. There are a wide variety of strategies out there, but the simplest starting point is to, give enough access to get the job done. E.g. sales managers don't need access to customize fields or create entities. They should be given access to only manage sales-related entities.

Having Strong Passwords & Using Password Manager
The easiest defence from being hacked is to use a strong password. This reduces security risks and having a secure password with a strong password combination increases the time it takes to crack the password.
A strong password should comprise symbols, letters, numbers, lower case - upper case combination, that is at least longer than 6 characters. We would recommend testing password strength by using a website called https://howsecureismypassword.net.
Lastly, by using a password manager, the program can automatically generate a strong password and store the password in the database. There is no need to come up with creative passwords + remembering the password. (some might have a feature where it can work without an internet connection).

RELATED: 10 Questions About Salesforce
Report a Security Concern
You can report a security concern via [email protected].
Safety Health Check
As an admin, you can use Health Check to recognize and deal with prospective susceptibilities in your safety setups, all from a solitary web page. A recap rating demonstrates how your org steps versus a protection standard, like the Salesforce Baseline Standard. You can publish as many as 5 personalized standards to use as opposed to the Salesforce Baseline Standard.

RELATED: Salesforce NPSP: Features & Pricing
Auditing
Auditing offers information regarding the use of the system, which can be vital in detecting real or possible security concerns. The Salesforce auditing attributes do not safeguard your organization by themselves; someone in your organization must do regular audits to identify potential abuse.
To confirm that your system is really protected, you should carry out audits to keep track of unforeseen changes or use fads.

Login History
You can review a list of successful and failed login attempts to your organization for the past six months. See Monitor Login History.

RELATED: Choosing the Right Salesforce Consulting Firm
Field History Tracking
You can additionally make it possible for auditing for individual fields, which will immediately track any modifications. Auditing is offered for all personalized things; just some typical things enable field-level bookkeeping. See Field History Tracking.
Arrangement Audit Trail
Administrators can additionally watch a Setup Audit Trail, which logs when alterations are made to your company's setup. See Monitor Setup Changes with Setup Audit Trail.

RELATED: A Brief Overview of Salesforce Lightning
Salesforce Shield
Salesforce Shield is a triad of safety and security devices that assists admins. Programmers also develop additional degrees of count on conformity and administration right into business-critical applications. It consists of Shield Platform Encryption, Event Monitoring, and also Field Audit Trail. Ask your Salesforce manager if Salesforce Shield is readily available in your company.

Monitor Login History
As an admin, you can check all login tries to your Salesforce org and Experience Cloud websites. The Login History web page turns up to 20,000 documents of customer logins for the past 6 months. To see even more documents, download and install the info to CSV or GZIP documents.

RELATED: Salesforce Commerce Cloud Pricing
Field History Tracking
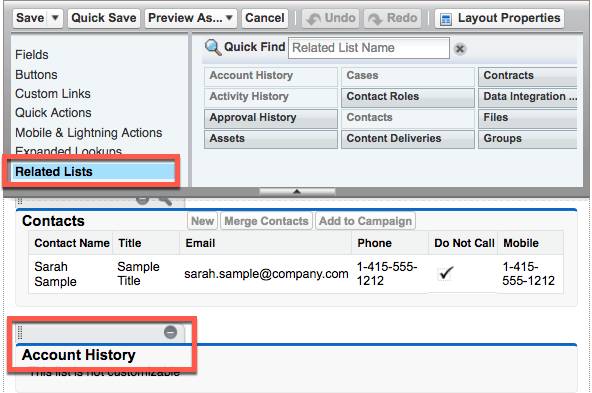
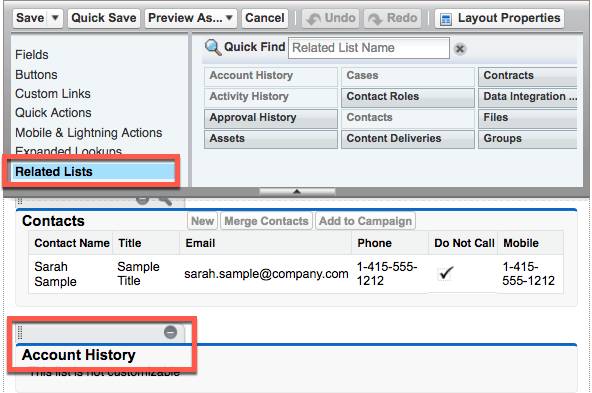
You can choose specific areas to track and present the area background in the History associated checklist of an item. Area background information is maintained for approximately 18 months with your org and 24 months using the API. Area background monitoring information does not count versus your Salesforce org's information storage space restrictions.
Readily available in Salesforce Classic (not readily available in all organizations), Lightning Experience, and also the Salesforce application
Real-Time Event Monitoring
Real-Time Event Monitoring aids you check and also discover basic occasions in Salesforce in close to real-time. You can keep the occasion information for bookkeeping or reporting functions. You can produce purchase protection plans utilizing Condition Builder-- a point-and-click device-- or Apex code.
Readily available in Enterprise, Unlimited, and Developer Editions Needs Salesforce Shield or Salesforce Event Monitoring add-on registrations.
With Real-Time Event Monitoring, gain higher understandings right into:
- Monitor online transactions.
- Monitor malicious activity (Unknown IP addresses).
- Monitor cloud security.

Conclusion
Obviously, this isn't an exhaustive list, but this should be a good starting point to keep your Salesforce secure. Implement these practices to give yourself a competitive edge against hackers.
.svg)